Alert Logic

The Sumo Logic app for Alert Logic provides enhanced security operations by seamlessly combining the capabilities of Alert Logic's incident detection and response with Sumo Logic's advanced log management and analytics platform. This powerful integration allows you to gain comprehensive insights into your security landscape, detect potential threats, and respond effectively to security incidents.
Key features of the Alert Logic app include:
- Real-time Threat Visibility. Consolidate and visualize Alert Logic incident data alongside other relevant logs in Sumo Logic, providing a unified view of your security posture.
- Incident Analysis. Correlate Alert Logic incident data with other log sources to identify patterns, anomalies, and potential attack vectors.
- Custom Dashboards. Create tailored dashboards and visualizations to monitor specific Alert Logic incident types, threat trends, and security metrics.
- Proactive Threat Hunting. Leverage Sumo Logic's advanced search capabilities to proactively hunt for signs of compromise across your environment using Alert Logic incident data.
- Incident Response Collaboration. Enable cross-functional teams to collaborate efficiently by sharing relevant incident data from Alert Logic within the Sumo Logic platform.
- Automation and Orchestration. Build automated workflows and triggers based on Alert Logic incident data to streamline incident response processes.
- Enhanced Security Insights. Gain deeper insights into your security landscape by analyzing Alert Logic incidents to elevate your security posture, accelerate incident response, and effectively protect your organization against evolving threats
- Rapid Incident Detection. Leverage real-time correlation and alerts, to quickly detect and respond to potential security threats.
- Improved Incident Response. Empower your security teams to respond effectively to incidents by providing them with a holistic view of threat data and streamlined collaboration tools.
- Customizable Monitoring. Tailor the Alert Logic dashboard to your organization's security requirements to monitor the most relevant threat vectors.
- Scalable Threat Hunting. Scale your threat-hunting efforts by leveraging Sumo Logic's powerful search capabilities to hunt for threats across large volumes of data.
Log types
This app uses Sumo Logic’s Alert Logic webhook to collect Incident Events from the Alert Logic Platform.
Sample log messages
Refer to Alert Logic guide for sample Incident Payload.
Sample queries
_sourceCategory=alertlogic
| json "extra.status", "extra.class", "incident.threatRating", "updatetime_str", "victim", "attacker", "incident.recommendations", "incident.description","incident.summary", "incidentId", "asset_deployment_type", "customer", "accountId" as status, incident_class, threat_rating, timestamp, victim, attacker, recommendations, description, summary, incident_id, deployment_name, customer_name, account_id nodrop
| json "extra.target_host", "extra.investigation_report", "extra.class", "extra.incidentUrl", "mitre_classification[*].technique", "mitre_classification[*].tactic" as target_host, investigation_report, incident_class, incident_url, mitre_technique, mitre_tactic nodrop
| json field=attacker "ip" as attacker_ip
| json field=_raw "attacker_country_name" as attacker_location
Set up collection
Follow the instructions for setting up Webhook connection to Sumo Logic from your Alert Logic console. The Sumo Logic app for Alert Logic uses the Incident schema for queries and dashboards.
Installing the Alert Logic app
This section has instructions for installing the Sumo Logic app for Alert Logic.
To install the app, do the following:
Next-Gen App: To install or update the app, you must be an account administrator or a user with Manage Apps, Manage Monitors, Manage Fields, Manage Metric Rules, and Manage Collectors capabilities depending upon the different content types part of the app.
- Select App Catalog.
- In the 🔎 Search Apps field, run a search for your desired app, then select it.
- Click Install App.
note
Sometimes this button says Add Integration.
- Click Next in the Setup Data section.
- In the Configure section of your respective app, complete the following fields.
- Field Name. If you already have collectors and sources set up, select the configured metadata field name (eg _sourcecategory) or specify other custom metadata (eg: _collector) along with its metadata Field Value.
- Click Next. You will be redirected to the Preview & Done section.
Post-installation
Once your app is installed, it will appear in your Installed Apps folder, and dashboard panels will start to fill automatically.
Each panel slowly fills with data matching the time range query received since the panel was created. Results will not immediately be available but will be updated with full graphs and charts over time.
Viewing Alert Logic dashboards
All dashboards have a set of filters that you can apply to the entire dashboard. Use these filters to drill down and examine the data to a granular level.
- You can change the time range for a dashboard or panel by selecting a predefined interval from a drop-down list, choosing a recently used time range, or specifying custom dates and times. Learn more.
- You can use template variables to drill down and examine the data on a granular level. For more information, see Filtering Dashboards with Template Variables.
- Most Next-Gen apps allow you to provide the scope at the installation time and are comprised of a key (
_sourceCategoryby default) and a default value for this key. Based on your input, the app dashboards will be parameterized with a dashboard variable, allowing you to change the dataset queried by all panels. This eliminates the need to create multiple copies of the same dashboard with different queries.
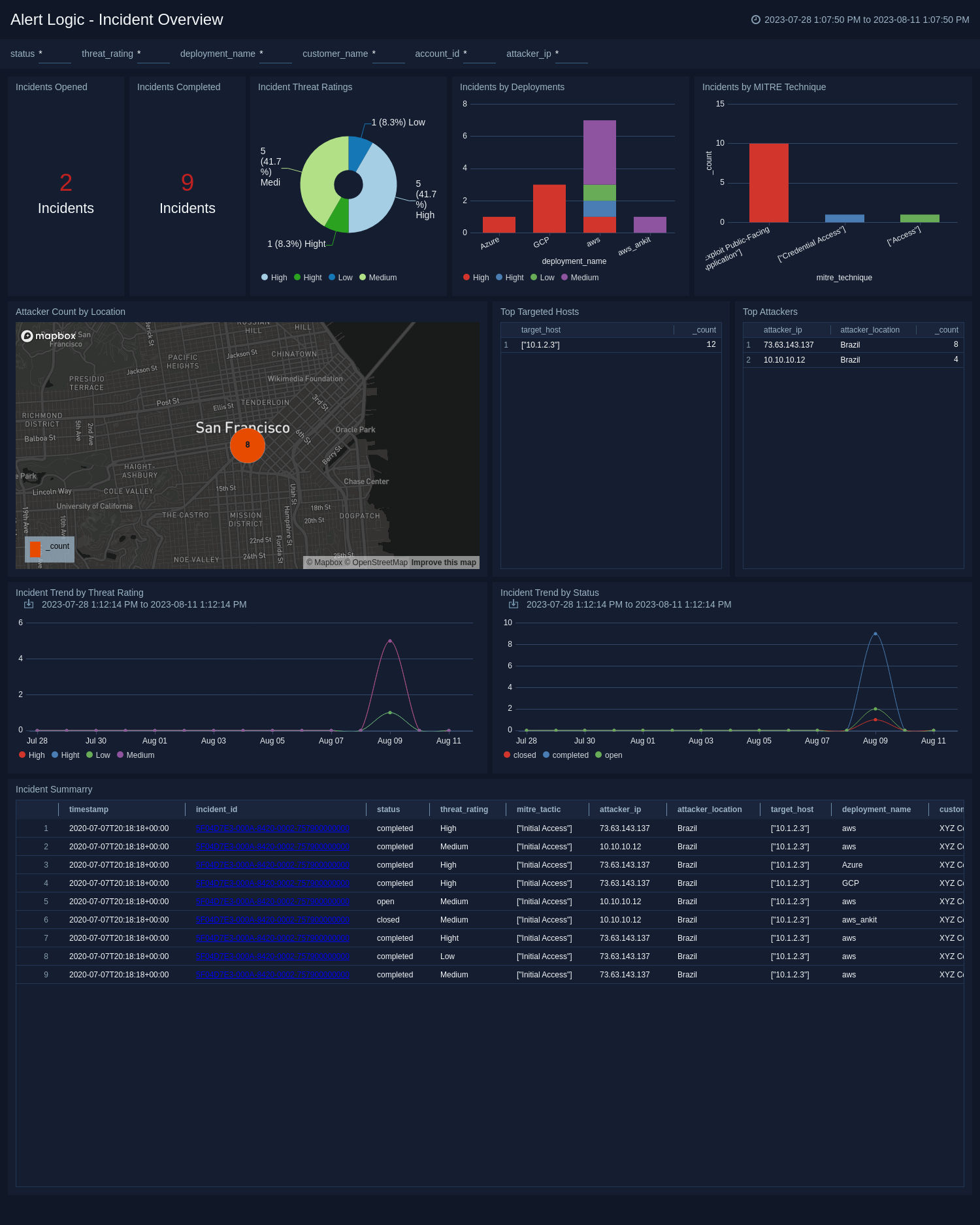
Overview
The Alert Logic - Overview dashboard provides a holistic view of your organization's cybersecurity landscape crafted to elevate your security operations. This dashboard empowers you with comprehensive insights into incidents, enabling the detection of potential threats and the execution of efficient responses to security incidents.
Upgrade/Downgrade the Alert Logic app (Optional)
To update the app, do the following:
Next-Gen App: To install or update the app, you must be an account administrator or a user with Manage Apps, Manage Monitors, Manage Fields, Manage Metric Rules, and Manage Collectors capabilities depending upon the different content types part of the app.
- Select App Catalog.
- In the Search Apps field, search for and then select your app.
Optionally, you can identify apps that can be upgraded in the Upgrade available section. - To upgrade the app, select Upgrade from the Manage dropdown.
- If the upgrade does not have any configuration or property changes, you will be redirected to the Preview & Done section.
- If the upgrade has any configuration or property changes, you will be redirected to the Setup Data page.
- In the Configure section of your respective app, complete the following fields.
- Field Name. If you already have collectors and sources set up, select the configured metadata field name (eg _sourcecategory) or specify other custom metadata (eg: _collector) along with its metadata Field Value.
- Click Next. You will be redirected to the Preview & Done section.
Post-update
Your upgraded app will be installed in the Installed Apps folder and dashboard panels will start to fill automatically.
See our Release Notes changelog for new updates in the app.
To revert the app to a previous version, do the following:
- Select App Catalog.
- In the Search Apps field, search for and then select your app.
- To version down the app, select Revert to < previous version of your app > from the Manage dropdown.
Uninstalling the Alert Logic app (Optional)
To uninstall the app, do the following:
- Select App Catalog.
- In the 🔎 Search Apps field, run a search for your desired app, then select it.
- Click Uninstall.