Microsoft Graph Security API Source
The Microsoft Graph Security API Source provides a secure endpoint to receive alerts from the Microsoft Graph Security API endpoint. It securely stores the required authentication, scheduling, and state tracking information. One threat event is reported for each affected device.
Data collected
| Polling Interval | Data |
|---|---|
| 5 min | Alerts |
Setup
Vendor configuration
You need to create and register a service application within the Azure Active Directory portal. The user creating the service application does not need to be an administrator, however, an administrator will be needed to grant the application the appropriate permissions to the Graph Security API.
The following steps show you how to create a service application:
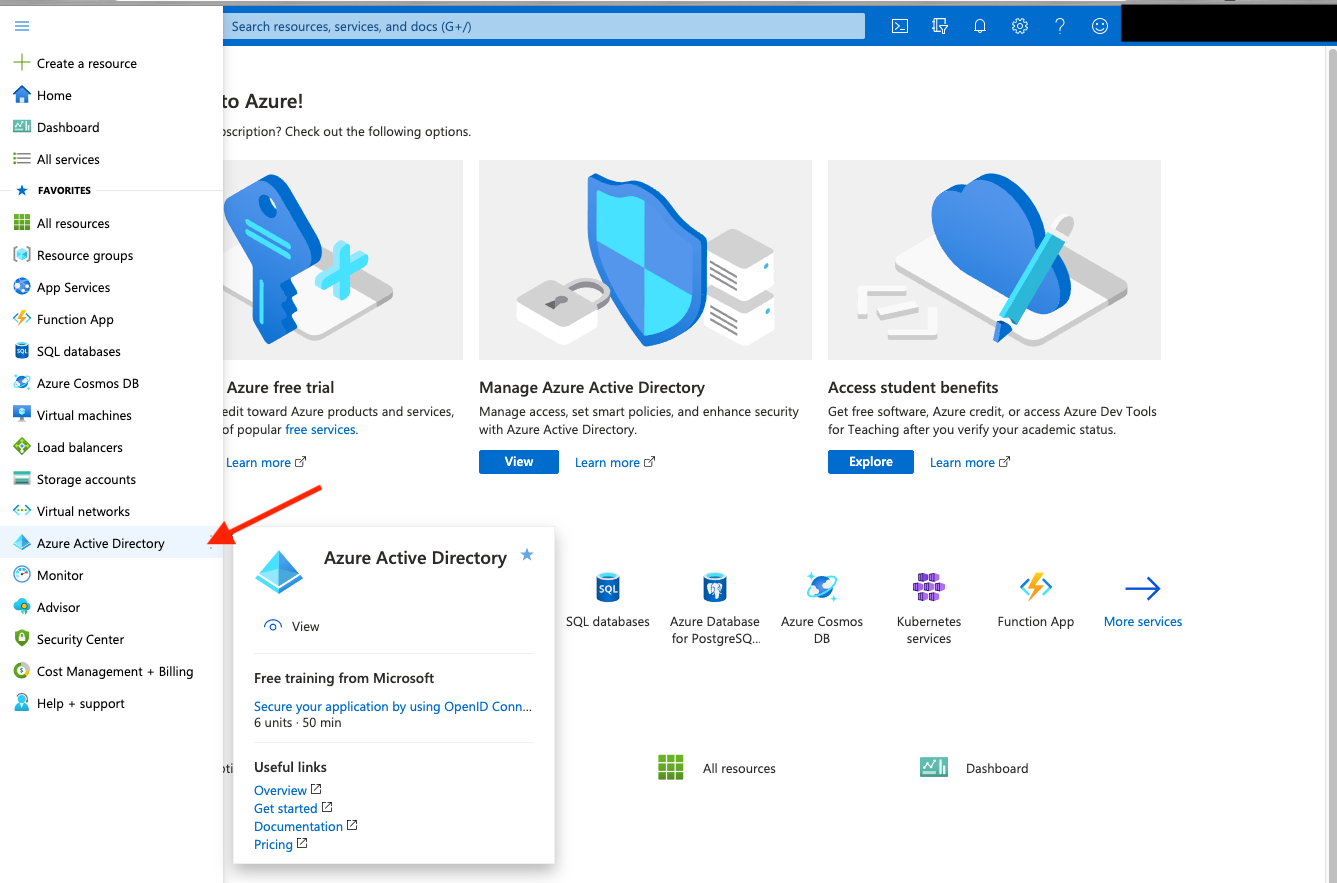
- Log into the Azure Active Directory Portal
- Select Azure Active Directory in the left menu.
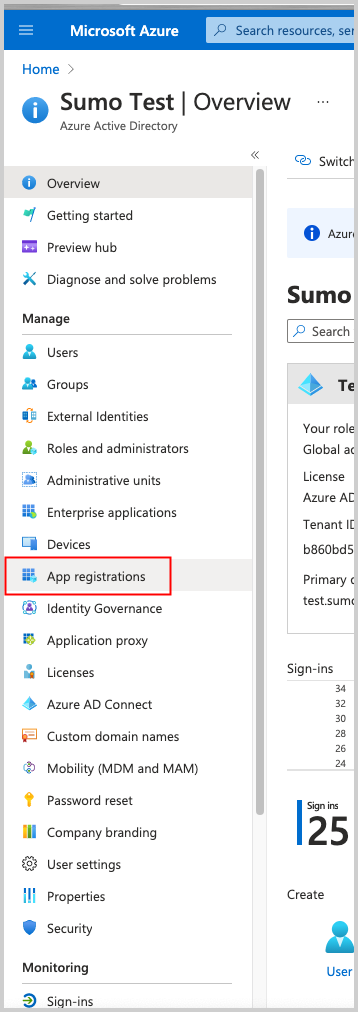
- Select App Registrations.
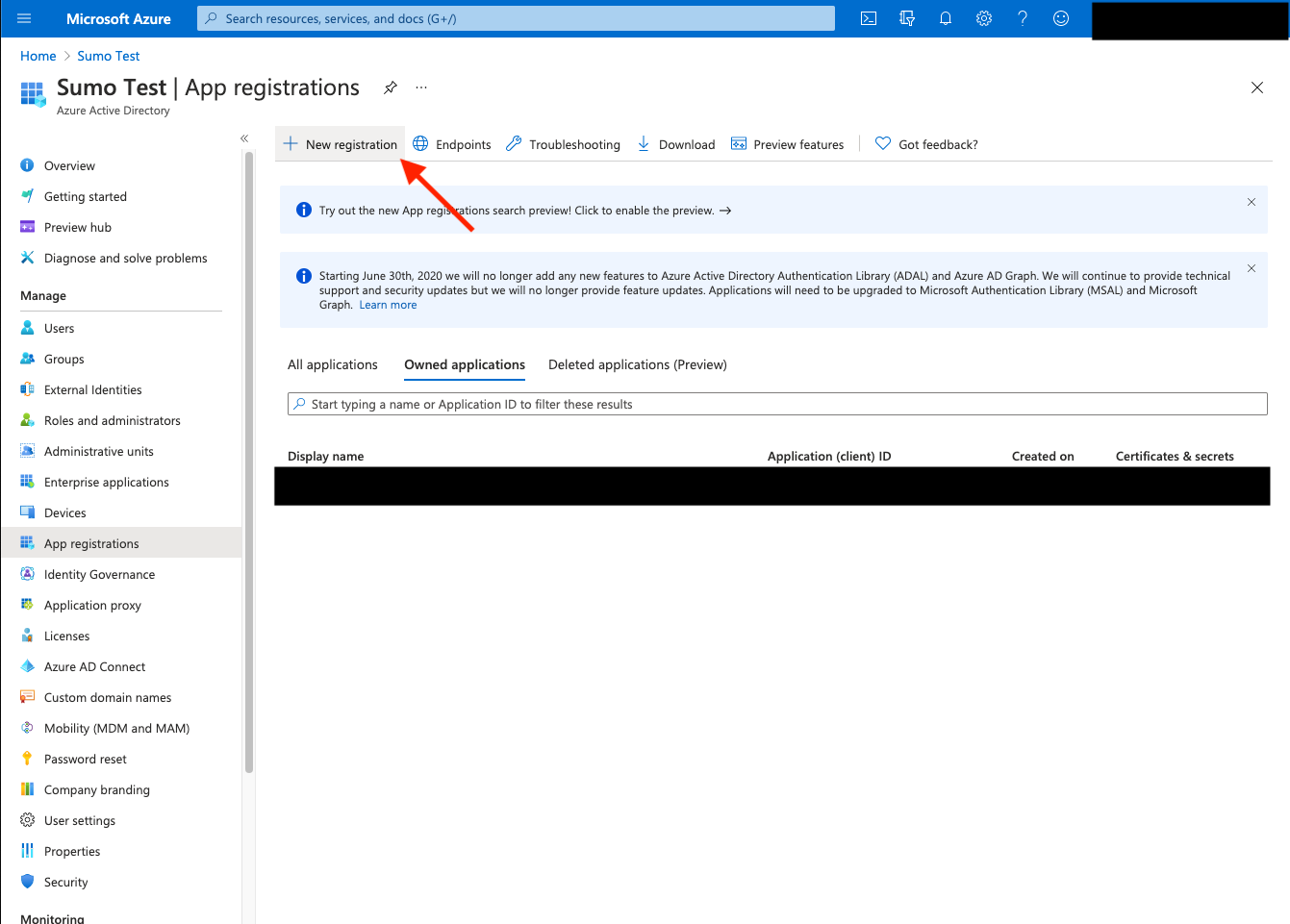
- Select New Registration. Go through the registration process, providing a name for the application. Selecting Accounts in this organizational directory only is sufficient.
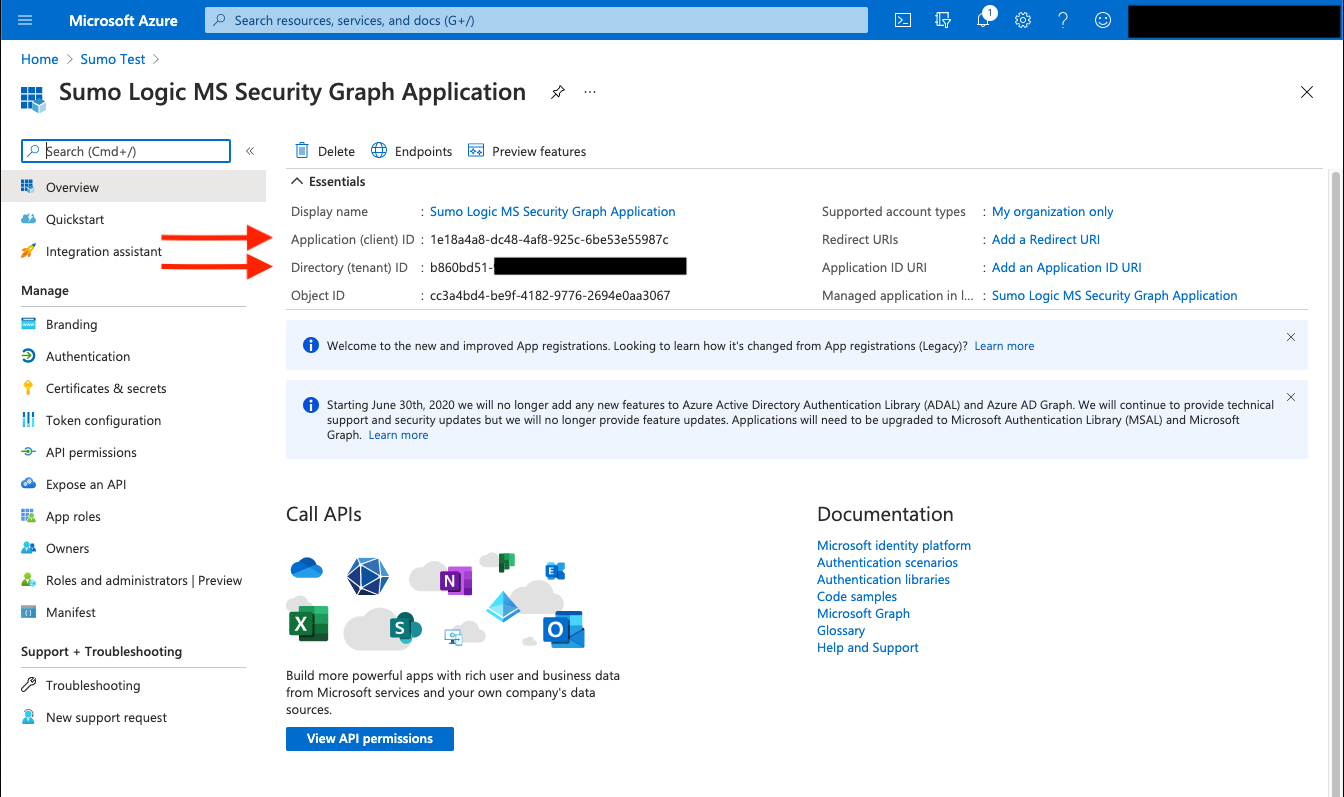
- After the application is registered ensure you copy the Application (client) ID and Directory (tenant) ID displayed on the Overview page. These are needed when creating the Source in Sumo Logic.
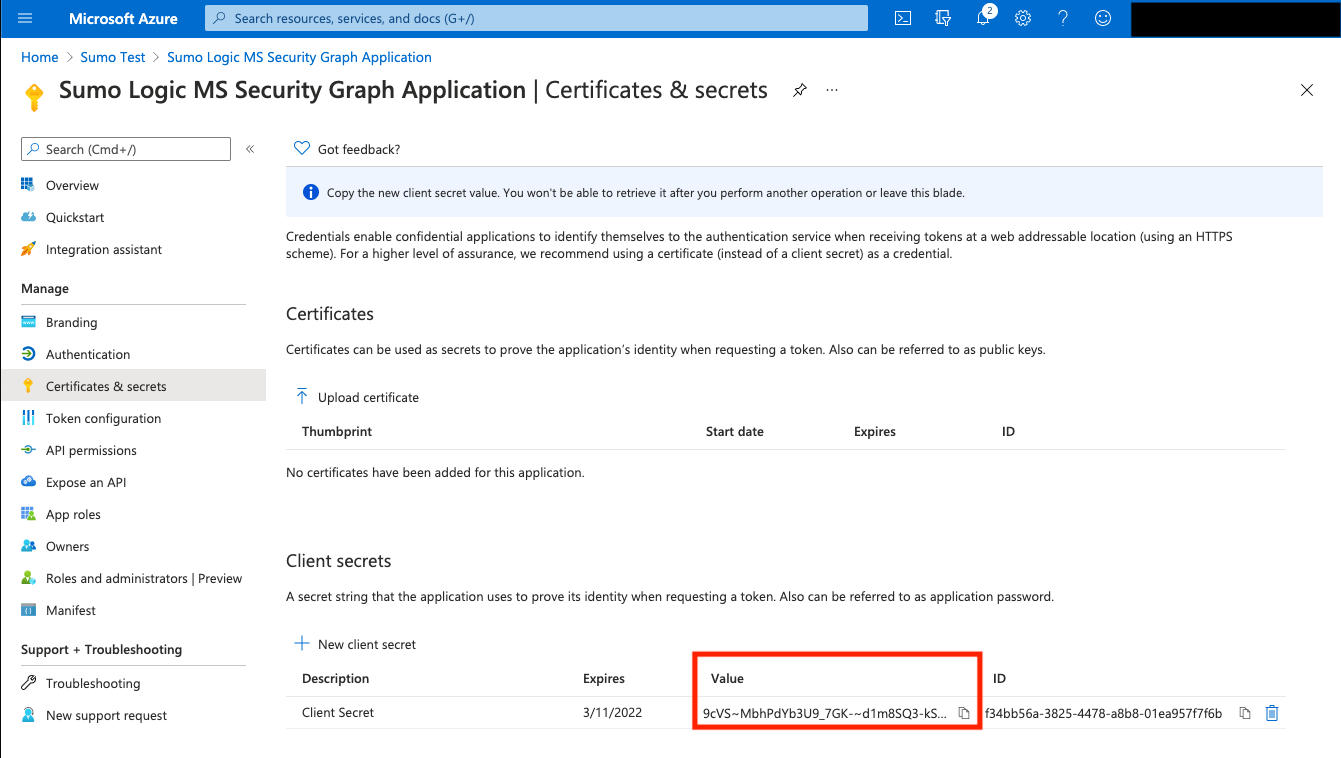
- Within the application configuration page, select Certificates and Secrets and create an Application Client Secret Key.
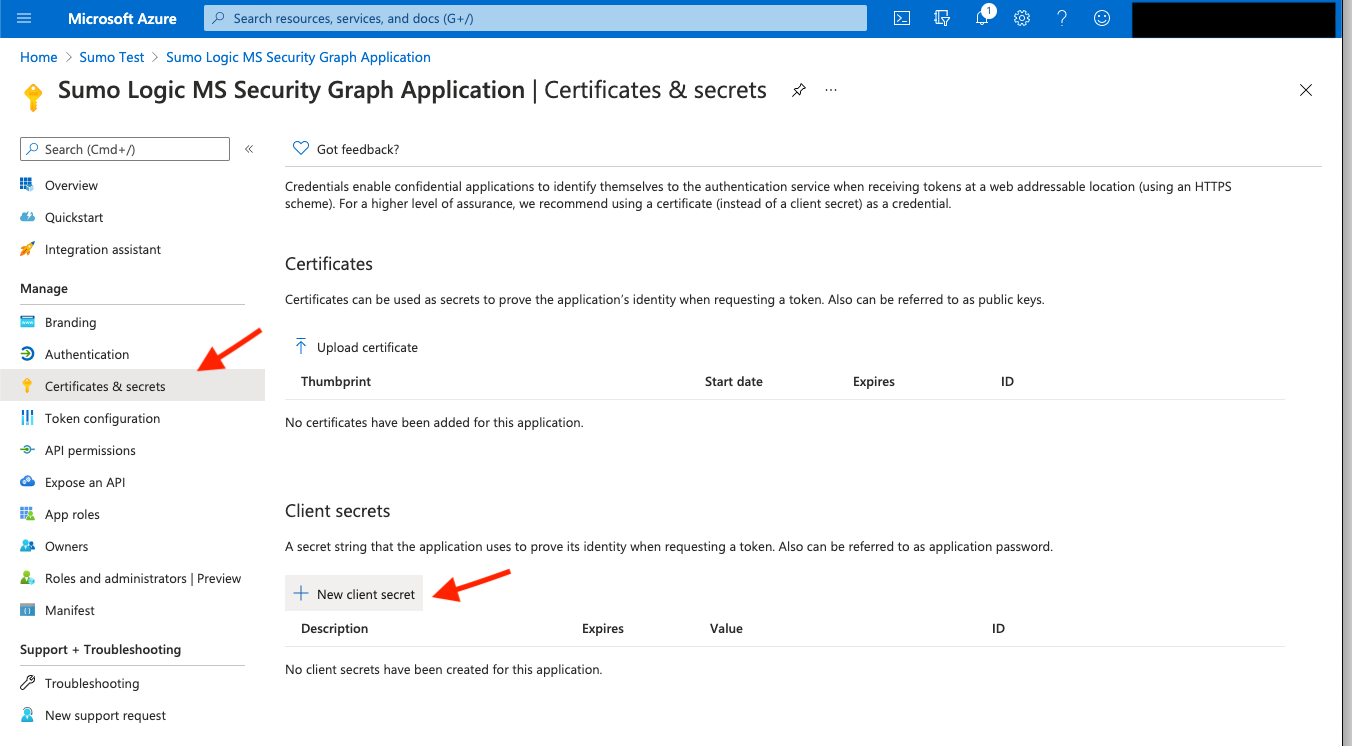
- Copy the Client Secret value, you'll need it when creating the Source in Sumo Logic.
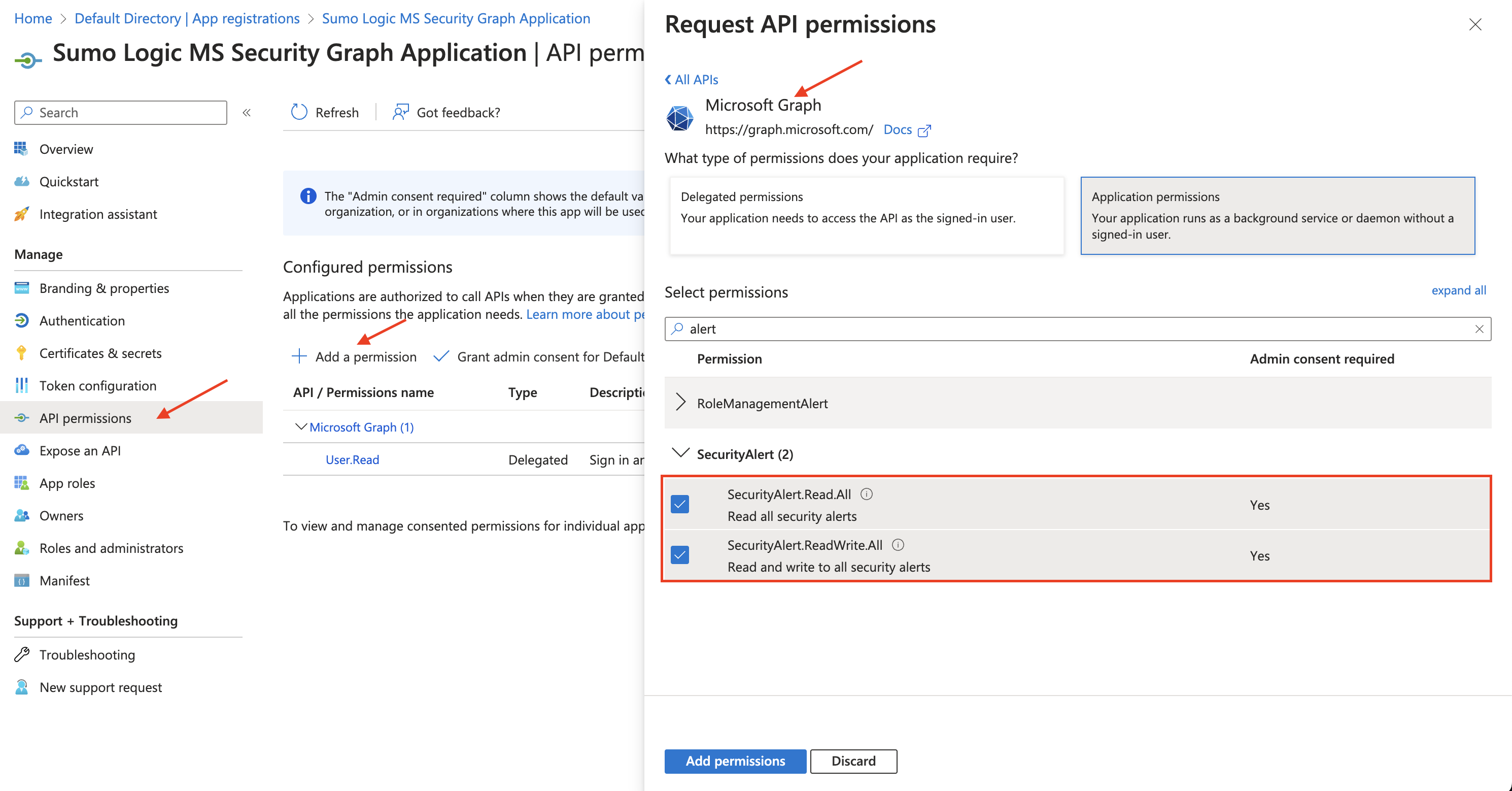
- Request the appropriate permissions for the application. Click on API Permissions, then Add a permission and select Microsoft Graph.
You need to find and select the SecurityAlert.Read.All, SecurityIncident.Read.All, and SecurityEvents.Read.All permissions. See this list to view all available security permissions.
note
An Administrator must approve (grant) these permissions before the Source will function.
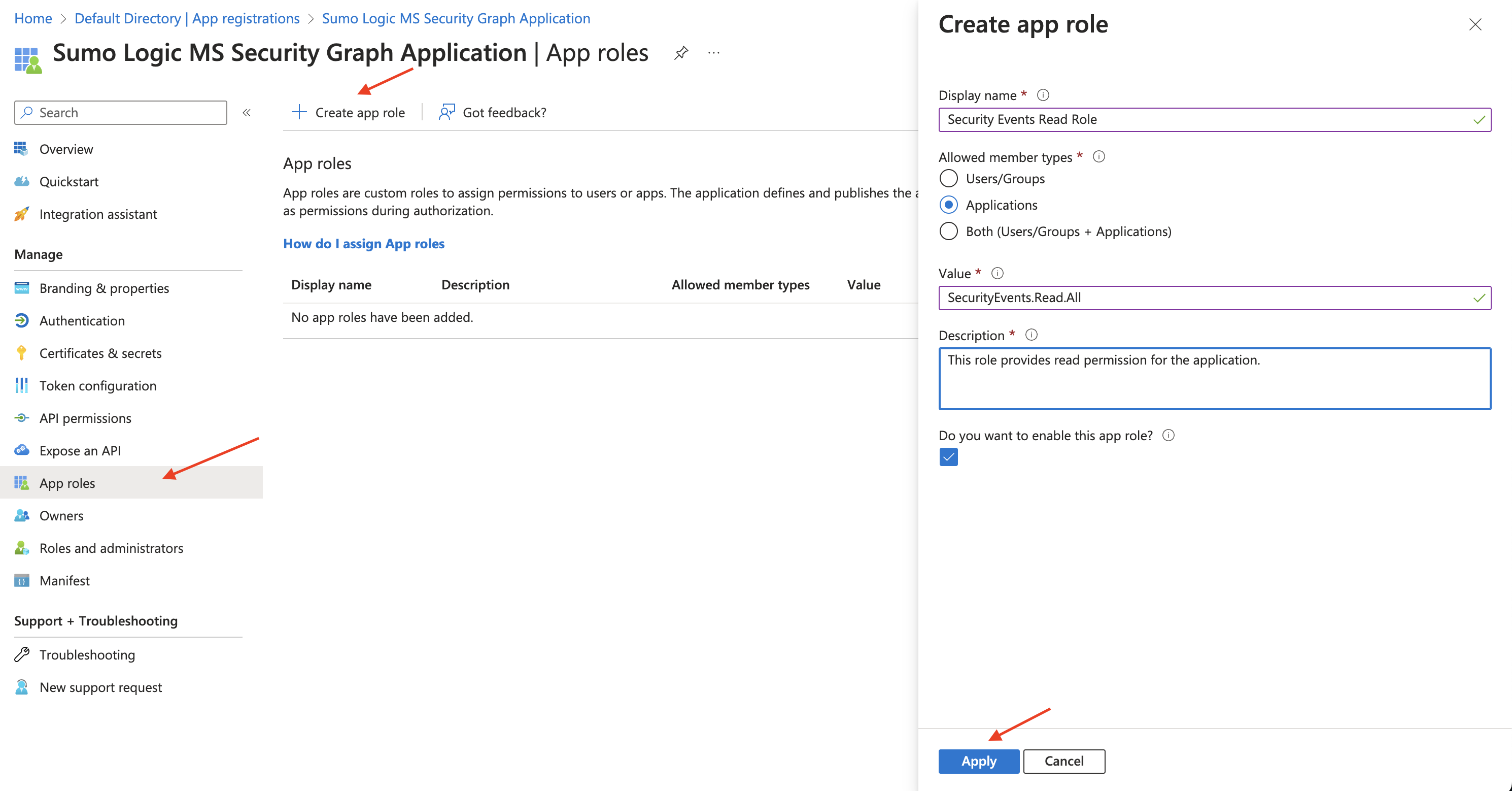
- Follow the steps below to enable the Application permission role.
- In the Manage menu, select App roles.
- Click the Create app role tab.
- Display name. Enter the display name for the role.
- Allowed member types. Select Applications as the allowed member type.
- Value. Enter
SecurityAlert.Read.Allas the value. - Description. Enter a brief description.
- Select the checkbox to enable the app role.
- Click Apply.
Source configuration
When you create a Microsoft Graph Security API Source, you add it to a Hosted Collector. Before creating the Source, identify the Hosted Collector you want to use or create a new Hosted Collector. For instructions, see Configure a Hosted Collector.
To configure a Microsoft Graph Security API Source:
- Classic UI. In the main Sumo Logic menu, select Manage Data > Collection > Collection.
New UI. In the Sumo Logic top menu select Configuration, and then under Data Collection select Collection. You can also click the Go To... menu at the top of the screen and select Collection. - On the Collectors page, click Add Source next to a Hosted Collector.
- Search for and select Microsoft Graph Security API.
- Enter a Name for the Source. The description is optional.
- (Optional) For Source Category, enter any string to tag the output collected from the Source. Category metadata is stored in a searchable field called
_sourceCategory. - Forward to SIEM. Check the checkbox to forward your data to Cloud SIEM. note
Select Forward to SIEM only if you have Cloud SIEM installed.
- (Optional) Fields. Click the +Add Field link to define the fields you want to associate, each field needs a name (key) and value.
A green circle with a check mark is shown when the field exists in the Fields table schema.
An orange triangle with an exclamation point is shown when the field doesn't exist in the Fields table schema. In this case, an option to automatically add the nonexistent fields to the Fields table schema is provided. If a field is sent to Sumo that does not exist in the Fields schema it is ignored, known as dropped.
- Enter the Directory (tenant) ID, Application (client) ID, and Application Client Secret Value you got from the Application you created in the Vendor configuration section.
- The Polling Interval is set to 5 minutes by default. You can adjust it based on your needs.
- Processing Rules for Logs. Configure any desired filters, such as allowlist, denylist, hash, or mask, as described in Create a Processing Rule.
- When you are finished configuring the Source, click Submit.
Base URL
Internally, the source will use the following base URL depending on the respective cloud region:
| BASE_URL | Value |
|---|---|
| Azure Government | https://graph.microsoft.us |
| Azure Global Service | https://graph.microsoft.com |
Metadata fields
| Field | Value | Description |
|---|---|---|
_siemForward | (true | false) | Set to true when Forward To SIEM is checked. |
_siemVendor | Microsoft | Set when Forward To SIEM is checked. |
_siemProduct | Graph Security API | Set when Forward To SIEM is checked. |
_siemFormat | JSON | Set when Forward To SIEM is checked. |
_siemEventID | {{category}} | This field is dynamically set based on the value of the category key in the log. |
JSON schema
Sources can be configured using UTF-8 encoded JSON files with the Collector Management API. See how to use JSON to configure Sources for details.
| Parameter | Type | Value | Required | Description |
|---|---|---|---|---|
| schemaRef | JSON Object | {"type":"Microsoft Graph Security API"} | Yes | Define the specific schema type. |
| sourceType | String | "Universal" | Yes | Type of source. |
| config | JSON Object | Configuration object | Yes | Source type specific values. |
Configuration Object
| Parameter | Type | Required | Default | Description | Example |
|---|---|---|---|---|---|
| name | String | Yes | null | Type a desired name of the source. The name must be unique per Collector. This value is assigned to the metadata field _source. | "mySource" |
| description | String | No | null | Type a description of the source. | "Testing source" |
| category | String | No | null | Type a category of the source. This value is assigned to the metadata field _sourceCategory. See best practices for details. | "mySource/test" |
| fields | JSON Object | No | null | JSON map of key-value fields (metadata) to apply to the Collector or Source. Use the boolean field _siemForward to enable forwarding to SIEM. | {"_siemForward": false, "fieldA": "valueA"} |
| tenant_id | String | Yes | null | The Directory (tenant) ID of the Azure AD application. | |
| secret_key | Boolean | Yes | null | The Application Client Secret Key created with access to the Azure AD application. | |
| application_id | String | Yes | null | The Application (client) ID of the Azure AD application. | |
| azure_gov | Boolean | No | false | Set to true if Azure tenant uses Azure Government region. | |
| polling_interval | Integer | Yes | 5 | This sets how many minutes the Source checks for new data. |
JSON example
loading...
Terraform example
loading...
FAQ
Click here for more information about Cloud-to-Cloud sources.